When people hear data breach, they still imagine the big scene 👀 a black screen, red warning text, some attacker sitting in the dark, maybe ransomware, maybe a zero day, maybe tomorrow’s headline.

But honestly, that is not how many breaches begin.
A lot of them start in the most boring way imaginable 😅 with a file sent to a private email address, a document uploaded to a personal cloud account, a sharing link opened a little too wide, or the right attachment sent to the wrong person.
No dramatic hacker soundtrack, no cinematic chaos, just a completely normal action that quietly turns into a security problem.
And that is exactly what makes modern data loss so tricky. It does not always kick the door in 💥 like a movie scene. Quite often, it simply walks out disguised as business as usual.
Verizon’s 2025 Data Breach Investigations Report gives that idea real weight: human involvement appears in 60% of breaches.
Verizon DBIR 2025
That should change how we talk about security. Once people are part of most incidents, the story is no longer only about attackers getting in, but also about data quietly getting out.
The breach does not always begin with malware
That is the uncomfortable part.
In many organizations, the first risky action is not malware, not an exploit, not even something that looks obviously malicious. It is convenience 📩

Someone sends a file to their private mailbox because they want to finish work later. Someone uploads a document to a personal cloud service because it feels faster. Someone shares a link externally because collaboration needs to move. Someone is about to leave the company and suddenly starts collecting information they no longer really need.
From the user’s point of view, this often does not feel like a breach in the making. From a data protection point of view, it can be exactly that.
Microsoft describes this area in Purview Insider Risk Management around risks such as data leakage and IP theft, which is precisely why this conversation matters so much in the Microsoft 365 world. The risk is often not some spectacular outside attack. The risk is that normal user behavior becomes the perfect vehicle for sensitive data to leave the business.
Five very normal ways data walks out of the business
- Sensitive content sent to a private email address
- Uploading files to personal cloud services
- Oversharing through SharePoint or OneDrive
- The wrong recipient, the wrong attachment, the wrong moment
- Data leaving with the insider

1. Sensitive content sent to a private email address
This is probably the most relatable scenario because almost everyone understands it instantly.
It does not look like exfiltration 🙃 it looks like convenience.
“I’ll just send it to myself quickly.”
And that is exactly the problem.
Microsoft Purview addresses this directly. In the Insider Risk documentation, Microsoft describes email exfiltration as detecting when users send sensitive assets outside the organization, including cases involving a personal email address.
That matters because it reframes the whole conversation. The risk is not always malware. Sometimes the risk is Outlook, a long day, and one bad decision disguised as a practical one.
2. Uploading files to personal cloud services
This is the next classic path ☁️ a file leaves the managed environment and lands in Dropbox, Google Drive, Box, or another private storage service.
Again, in the moment, it often feels practical rather than risky. Faster. Easier. Less friction. Maybe even harmless.
But that is exactly why it keeps happening.
Microsoft documents this scenario in Purview Endpoint DLP with activity coverage such as upload to a restricted cloud service domain. So this is not some obscure corner case. It is a known and expected route for potential data exfiltration.
And that is where the framing changes. The breach is no longer some distant attacker story. It becomes a browser action 🌐 a drag and drop, a quick upload, a shortcut taken between two meetings.
3. Oversharing through SharePoint or OneDrive
Not every leak is intentional. Some of them are just collaboration moving faster than control 🤝
A file is shared externally. A folder gets broader permissions than intended. A link is created for one purpose and quietly lives on for another.
This is why the old “protect the perimeter and hope for the best” approach no longer cuts it. In modern collaboration environments, the real question is not only where data is stored. The real question is how easily it can travel.
Microsoft’s Purview service descriptions reflect exactly that challenge: organizations are dealing with fragmented data, reduced visibility, and increasingly complex collaboration patterns. That is why classification, labeling, and DLP belong together. If protection only exists at the edge, the business will keep creating blind spots inside its own tools.
4. The wrong recipient, the wrong attachment, the wrong moment
Some incidents are technically boring and operationally awful 😬
The wrong person gets the email. The wrong attachment ends up in the thread. Someone clicks send too fast and notices the mistake too late.
These are not the incidents that make security teams feel glamorous. But they are exactly the ones that create reporting obligations, uncomfortable calls with legal, and a very bad Friday afternoon.
This is also where security has to become practical. Warnings in the right moment 💡 policy tips, prompts, friction where it actually helps.
Because the goal is not pretending users will stop making mistakes. The goal is designing controls around the fact that they will. And once again, that fits the Verizon finding perfectly: when human involvement appears in 60% of breaches, preventing bad everyday decisions is not a side topic. It is core security work.
5. Data leaving with the insider
Then there is the more deliberate version 🔍
A user is disengaged. A resignation is coming. Access still exists, but trust is already fading.
Microsoft’s Purview Insider Risk templates for departing users explicitly reference activity involving personal cloud messaging and storage services, alongside broader scenarios tied to data leakage and IP theft.
That is important because the exact same channels people use for convenience can also become channels for intentional loss.
The tricky part is that technology does not just need to spot clearly malicious behavior. It needs to notice when normal behavior starts becoming risky behavior, and when risky behavior starts turning into actual data loss.
Why this matters even more in the age of AI
This is where it gets interesting 🤖
AI does not replace these risks. In many cases, it amplifies them.
If one employee can manually forward a sensitive file to a private mailbox, AI can make it easier to find ten more. If one user can upload a confidential document to an unsanctioned service, AI can accelerate how quickly that content is summarized, repackaged, and redistributed. If one overprivileged identity already has too much access, agents can operationalize that access at scale.
That is why the conversation should not begin with futuristic panic about autonomous agents. It should begin with the very present reality that many organizations still struggle with ordinary exfiltration paths in email, browsers, endpoints, and collaboration platforms.
The future risk becomes so dangerous because the present risk is already so normal.
Why Microsoft Purview matters here
What makes Microsoft Purview relevant is not some vague promise of “better security.” It is that it addresses the actual routes data takes when it leaves the business 🧭
- Purview can help detect sensitive content sent outside the organization by email
- It can monitor or restrict uploads to risky cloud service domains
- It can classify and label content so protection stays attached to the data itself
- It can support insider risk investigations when behavior starts pointing toward leakage or IP theft
That is the shift many organizations still need to make.
A breach is not only an intrusion problem. Very often, it is a movement problem 📦
- Data moves
- People move
- Access moves
- Behavior changes
And by the time everyone realizes it, the incident may already be underway.
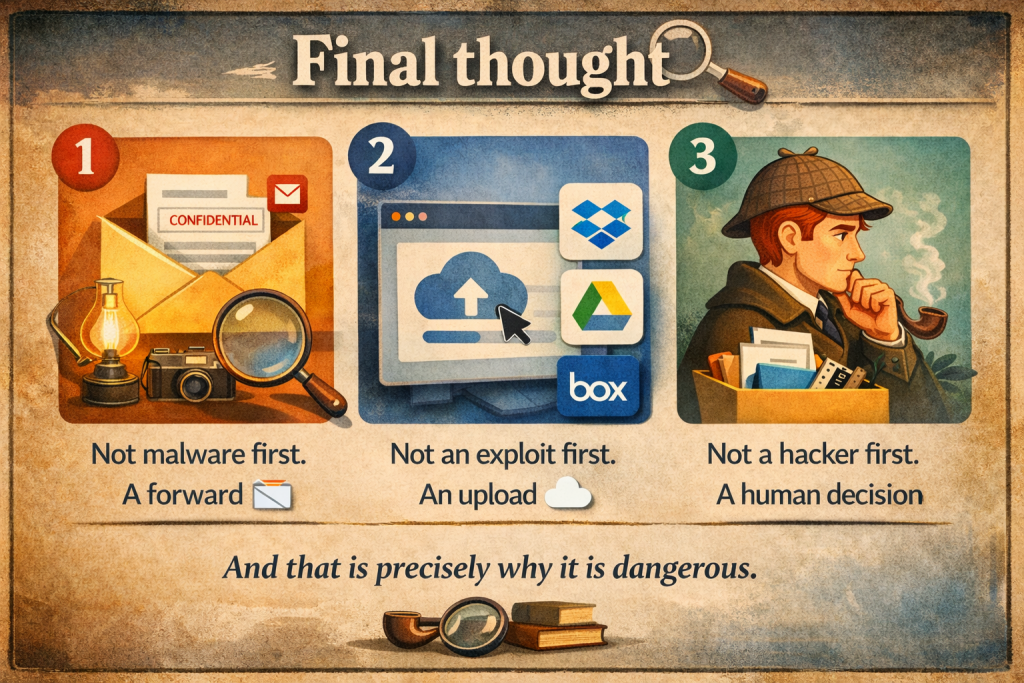
Final thought
The modern data breach often looks almost boring at first.
- Not malware first. A forward 📧
- Not an exploit first. An upload ☁️
- Not a hacker first. A human decision
And that is exactly why it is dangerous.
Because if data can leave through completely ordinary behavior, then protection has to live inside ordinary behavior too.
That is where the real work starts.

